Derren Brown’s Svengali Tour … Brilliant!
Last night (11/05/2011) I had the pleasure of going to see Derren Brown’s Svengali show at the Alexandra Theatre in Birmingham. Before I continue, I would like to say a big thanks to my wife for looking after our 6 week o...
Global Gestures … Don’t Get it Wrong
In my recent talk Social Engineering Like In the Movies – The Reality of Awareness and Manipulation I talk about how important it is to understand body language, especially in the right context. I also mention how even th...
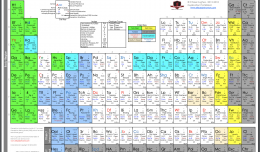
The Behavioural Table of Elements – Body Language
I recently became aware of a US based Intelligence and Behaviour Expert by the name of Chase Hughes. I picked up his book The Ellipsis Manual which has been a great addition to my collection of books and resources on body langu...
The Risks of Posting in Social Networks … By Trend Micro
I found this awesome Infograph put together by Trend Micro on the Risks o Posting in Social Networks. I cant remember exactly where I found it now but I saved the image so I am posting it here. If you know where it came from fe...
How To Install BeEF … Browser Exploitation Framework
The Browser Exploitation Framework (BeEF) is an excellent tool for Social Engineers and Pentesters. This video provides a quick How To on installing it under Linux. The install from start to finish takes around 10 minutes, but ...