Mind Reading … The Outer Body Experience
We have spoken before about the importance of commitment when it comes to social engineering and manipulation. The commitment to be the delivery guy, engineer and so on. However, I think there is another important skill to be s...
Going through Changes … Subliminal Hacking Arrives
You may be reading this message from the Head Hacker RSS Feed, and if so you will notice that www.headhacker.net is no more, and its now www.subliminalhacking.net (headhacker.net will always forward to here) First of all I want...
Social Compliance and Manipulation… The Art of Confidence
As human beings we are very good at making excuses, and always believing that some how we have it worse than the other guy. There is often that mentality that, its not we don’t want to do this or that, its just that ̷...
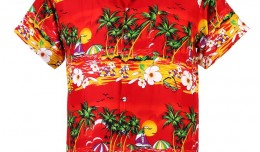
Hiding in plain sight… Playing it loud and proud
Happy New Year. 2011 has already gotten off to a hectic start for me, as I type this I am still in California working, but looking forward to flying back at the end of the week. In the last week I have tried out something a lit...
Merry Christmas and a Happy New Year Head Hackers… See you in 2011
Merry Christmas and a Happy New Year to everyone that reads this blog. Its been a great year, and I hope to bring your more enjoyable content next year. In 2010 I have done my best to give an informative post every week, ...